Gmail Accounts Hacking Risk 2012!
Millions of users use Gmail as their information center to perform actions such as Business, Chat, Place Orders, Payment confirmation, main password recovery mail for different web services and so on...
many people - including myself use Gmail to store and save important and personal data, none of us want our data to be at risk of steal, manipulation, and obviously not considering the Gmail account being completely hacked!
I found a possibility to do all that!
Fortunate enough for us, Google is taking a lot of efforts securing their services. mostly by doing a great job, which integrates supporting a vulnerability reward program.
I made a quick research and reported this vulnerability along with all the related details.
I must say Google's response was very quick and so as their fix. (it is Fixed)
as it appears here :Vulnerability Reward Program even after the bounty raise:
Google's Reward for this bug: $1337 (mail.google.com)
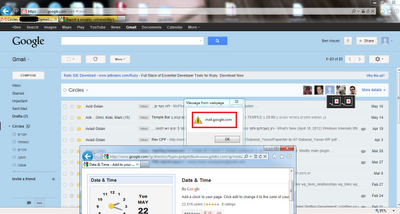
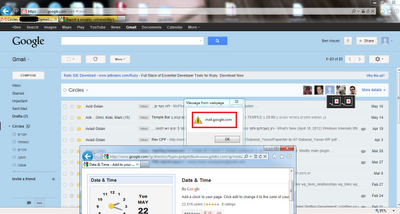
PoC Picture:
Technical Details:
I am quite busy at work and personal life at these days so I placed a side the reward programs of Google, Facebook And others.
many people - including myself use Gmail to store and save important and personal data, none of us want our data to be at risk of steal, manipulation, and obviously not considering the Gmail account being completely hacked!
I found a possibility to do all that!
Fortunate enough for us, Google is taking a lot of efforts securing their services. mostly by doing a great job, which integrates supporting a vulnerability reward program.
I made a quick research and reported this vulnerability along with all the related details.
I must say Google's response was very quick and so as their fix. (it is Fixed)
as it appears here :Vulnerability Reward Program even after the bounty raise:
Google's Reward for this bug: $1337 (mail.google.com)
PoC Picture:
Technical Details:
I am quite busy at work and personal life at these days so I placed a side the reward programs of Google, Facebook And others.
I was just checking my mail the other day and I noticed something different.
Google made this nice change in Gmail , apparently around December 2011 - Google Adds circles to Gmail
"Users can now Filter their Mails based on their Circles"
Trusting your Google+ Friends?
When I clicked this Gmail Circles feature, I saw my Google+ connections: profile pictures, nicknames and some other circles related data
Do they Control this data?! - Yes!
I had to spend some time back in the business, Gmail Stored XSS is a serious finding!
So I imminently researched that feature's JavaScript code.
It appeared that data that comes from Google+ was not sanitized by Gmail!
It appeared that data that comes from Google+ was not sanitized by Gmail!
zk.prototype.Ca = function $pn(a, c, d) { this.xa = 0;
if (!this.ea) { //Shorten/removed var e = this.Bb.zb().body, g = this.ea.va(); //Shorten/removed
e.wa = h } a: { if (d) switch (d.toLowerCase().split(",")[1]) { case "l": break a; case "r": /removed; break a } e = 2 } this.wa.setPosition(cka(d), e, i, -1); jc(this.ea.va(), "T-ays-avH"); ud(this.ea.va(), 0, 0); this.ea.Mc().innerHTML = c; //c = Data from Google+; this.wa.To(a); this.wa.Me(k, 0) };
This Gmail Code was creating a Tool-tip that Included profile circles information that comes from your Google Plus friend's account, if they used a payload, your mail account would have been at a serious risk.
Exploiting the Vulnerability - malicious Google+ Account.
As First it is important to note that Anyone that already got accepted as your friend in Google+ could trigger this attack on your Gmail account!
So all that is left is crafting a very nice Google+ account with some attractive profile, then after this evil account gets many friends/victims - Attack em all!
Google+ was and still is blocking the possibility of using a payload in the required field that was used to trigger this attack, but I found a way around it, sorry but I cannot reveal how I did that. (I am sure some of you pros might know how).
After I used my technique and crafted the Google+ evil profile it was possible to attack Gmail of all of that profile's friends!
PoC Picture:
As always I appreciate the opportunity to preserve my skills and gain some more experience
Thank you Google security team.
"Ben Hayak" - Google Security Hall of Fame Page
http://www.google.com/about/company/halloffame.html
PoC Picture:
Thank you Google security team.
"Ben Hayak" - Google Security Hall of Fame Page
http://www.google.com/about/company/halloffame.html



